RansomWhere?
Let’s generically thwart macOS ransomware with math. RansomWhere? continuously analyzes file entropy to identify encryption activity in real time, detecting suspicious processes and stopping ransomware before it can do serious damage.
Download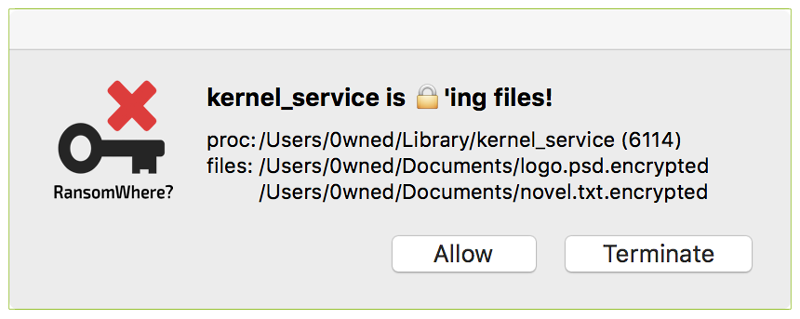
RansomWhere? is a utility with a simple goal: generically thwart Mac ransomware. It does so by identifying a behavior common to virtually all ransomware: the creation of encrypted files. Ransomware encrypts your personal files and then demands payment, the ransom, in exchange for the decryption key. If you refuse to pay and do not have backups, your files may be lost forever. That sucks.
RansomWhere? attempts to prevent this generically by detecting untrusted processes that begin encrypting files. Once such a process is identified, RansomWhere? immediately stops it and alerts the user. If the process is malicious, the user can terminate it. If it is a false positive, the user can allow it to continue and optionally create a rule to automatically allow it in the future.
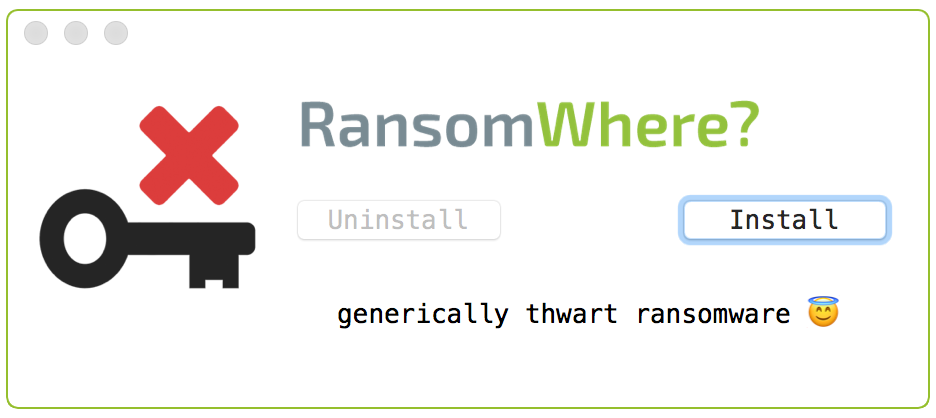
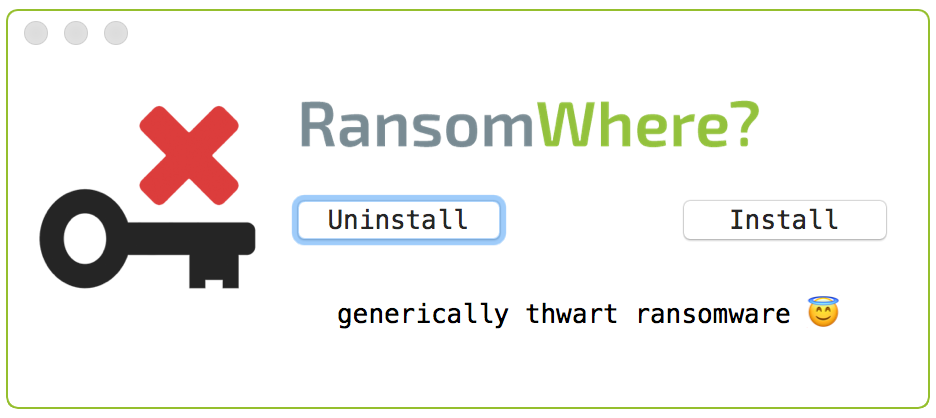
After downloading the latest version, extract it and run 'RansomWhere Installer.app' and press the 'Install' button:
Because RansomWhere? utilizes Apple’s Endpoint Security framework to monitor for the creation of encrypted files, it requires elevated system privileges. As such, during installation the operating system will display an authorization prompt.
Another requirement of the Endpoint Security framework, enforced by Apple, is Full Disk Access. The first time you install RansomWhere?, it will instruct you on how to manually grant it this permission.
- Click the 'Open System Setting' button
- In the "Full Disk Access" table, toggle the check box next to RansomWhere.app:
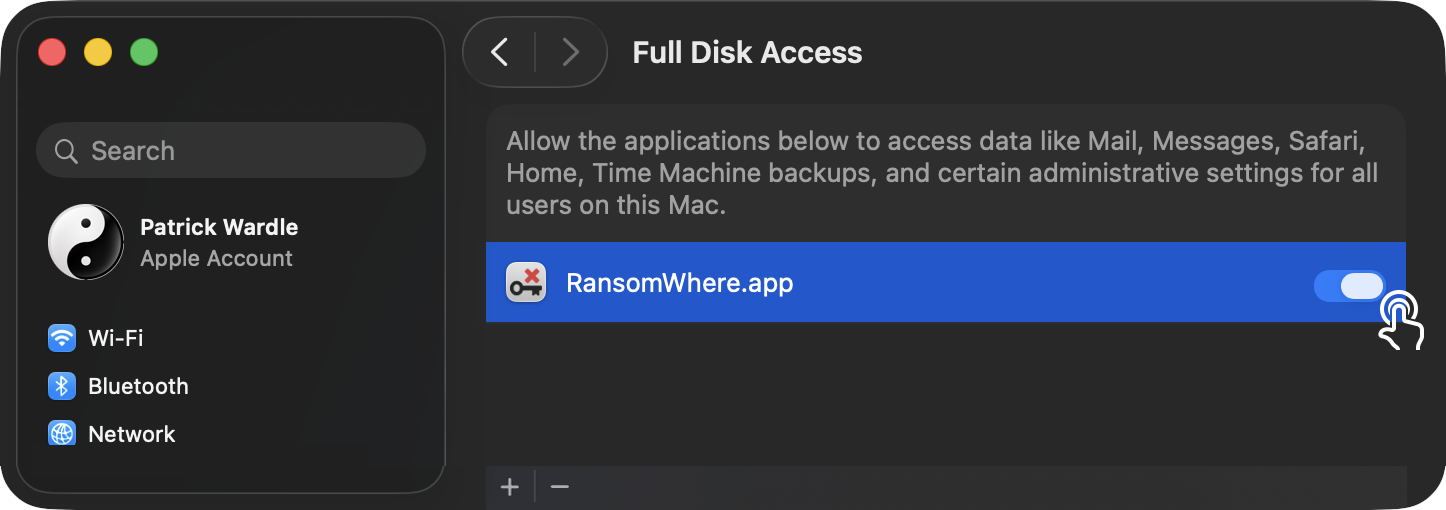
Note:
If RansomWhere? doesn't show up, click the '+' and add: /Library/Objective-See/RansomWhere/RansomWhere.app
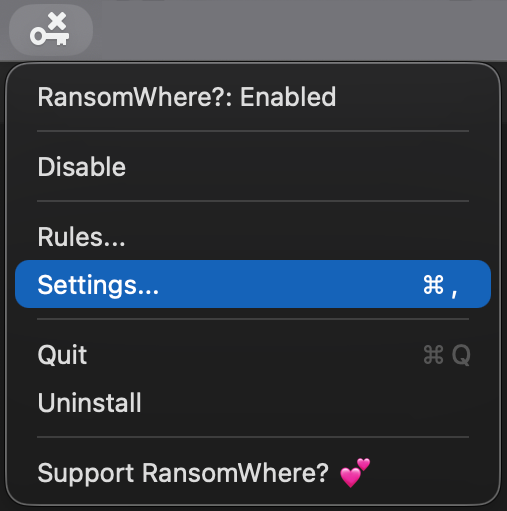
To uninstall RansomWhere, click on 'Uninstall RansomWhere?' in its status bar menu:
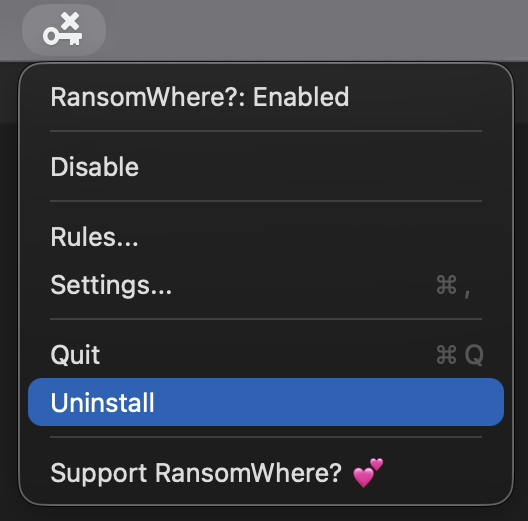
This will launch the uninstaller. Click 'Uninstall' to completely remove RansomWhere?:
Once installed, RansomWhere? will attempt to block any 3rd-party processes that are detected quickly creating encrypted files (a la ransomware). Specifically, it will suspend the suspect process and alert the user. For example; here's the alert for the Mac ransomware KeRanger:
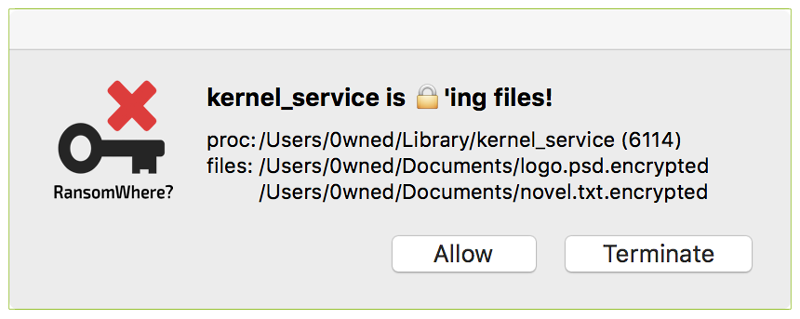
The alert contains information such as:
-
The process responsible for the action:
The alert contains the process name, pid, path, and any arguments. There are also clickable elements on the alert to show the process's code signing information, VirusTotal detections, and process ancestry. -
The list of encrypted files
The alert shows the list of files the program was observed rapidly encrypting.
Note:
By design, RansomWhere? will alert on any third-party process that it observes rapidly creating encrypted files. (If "Notarization Mode" is enabled, notarized applications will be trusted and allowed).
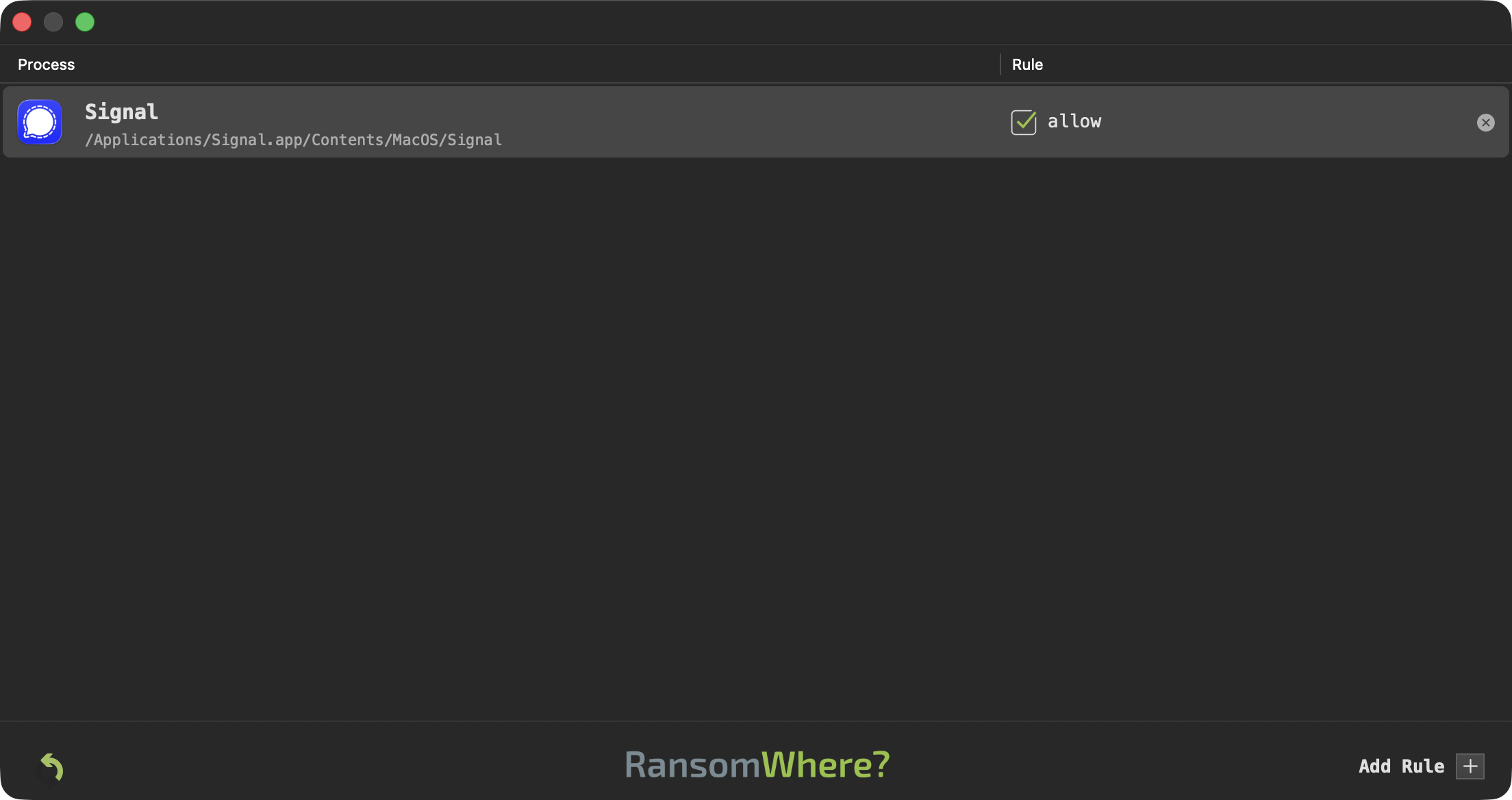
It is worth stressing that legitimate software may do this as well. Examples include encrypted messaging apps (such as Signal), browsers (such as Chrome updating its encrypted Safe Browsing data), or even security products (for example, antivirus tools installing encrypted signature files).
If you recognize the program, (always verify its code signing information in the alert window), then click "Allow" and, if "Remember my decision" is checked, a rule will be created so you will not be prompted again.
By design, RansomWhere? will alert on any third-party process that it observes rapidly creating encrypted files. (If "Notarization Mode" is enabled, notarized applications will be trusted and allowed).
It is worth stressing that legitimate software may do this as well. Examples include encrypted messaging apps (such as Signal), browsers (such as Chrome updating its encrypted Safe Browsing data), or even security products (for example, antivirus tools installing encrypted signature files).
If you recognize the program, (always verify its code signing information in the alert window), then click "Allow" and, if "Remember my decision" is checked, a rule will be created so you will not be prompted again.
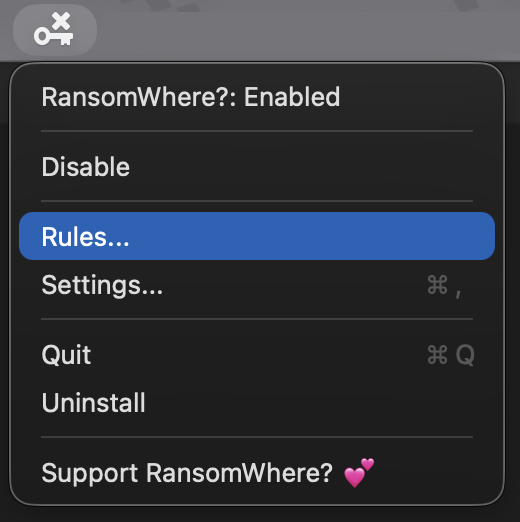
The rapid creation of encrypted files is either allowed or blocked, based on user input ...which are then turned into rules. To open the rules window, click on 'Rules' in RansomWhere?'s status bar menu:
The rules window displays these rules, as well as allows one to manually delete rules or add new ones:
There are preference options to control various aspects of RansomWhere? including its icon mode, notarization mode and to disable automatic update checks:
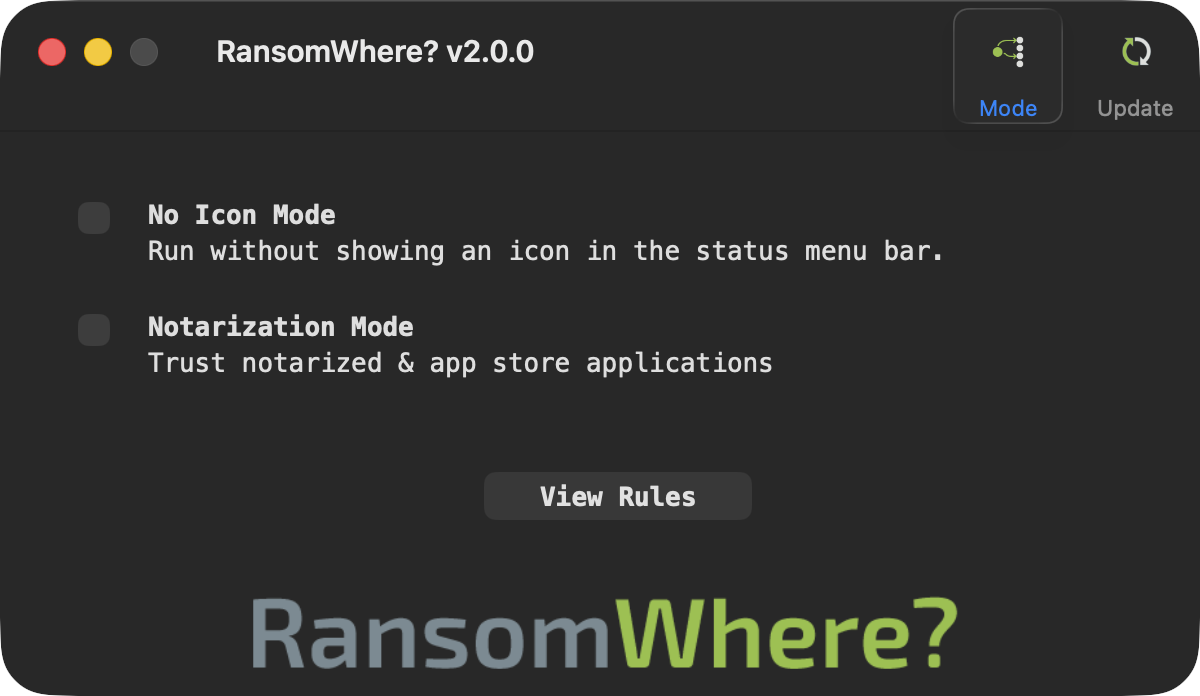
"Notarization Mode", if enabled, will ignore any notarized (or Mac App Store) application.
Frequently Asked Questions
Q: RansomWhere? displayed an alert. Is this ransomware?
A: To generically detect and thwart Mac ransomware, RansomWhere? alerts on any third-party program that rapidly creates encrypted files. As such, a flagged process is not necessarily ransomware. Carefully examine the alert. If you recognize and trust the process, as well as the files it is creating, simply click "Allow." If "Remember my decision" is checked, RansomWhere? will create a rule and ignore this process in the future.
Q: I installed RansomWhere? and knowingly ran some ransomware to test it. Why was it not detected?
A: First and foremost, if the ransomware is dormant or not actively encrypting files, RansomWhere? will not flag it. Detection occurs only once the ransomware is activated and begins encrypting files. For example, the KeRanger ransomware initially slept for several days and required an encryption key from its (now offline) command-and-control server before it began locking files.
Other reasons may include the fact that the encrypted files are created too slowly to trigger detection, or that the files do not appear sufficiently encrypted to meet RansomWhere?'s detection thresholds. All this, and more, is explained in the blog post 'Towards Generic Ransomware Detection?'.
Note: If you stream the system log with the following predicate, you can see exactly what RansomWhere? is doing and the decisions it is making:
log stream --level debug --predicate="subsystem='com.objective-see.ransomwhere'"
Note:
In RansomWhere?'s GitHub Repo, you will find various (safe) testing scripts that rapidly create encrypted files and will trigger RansomWhere? alerts.