Netiquette
In today’s interconnected world, it’s uncommon to find an application—or even malware—that doesn’t make use of the network. Netiquette is a network monitor that lets you explore all sockets and connections through an interactive UI or the command line.
Running Netiquette
First download Netiquette. Depending on your browser, you may need to manually unzip the application by double-clicking on the zipped archive.
There is no need to install anything, and Netiquette can be run from anywhere. (This also means there is nothing to uninstall, simple delete the application).
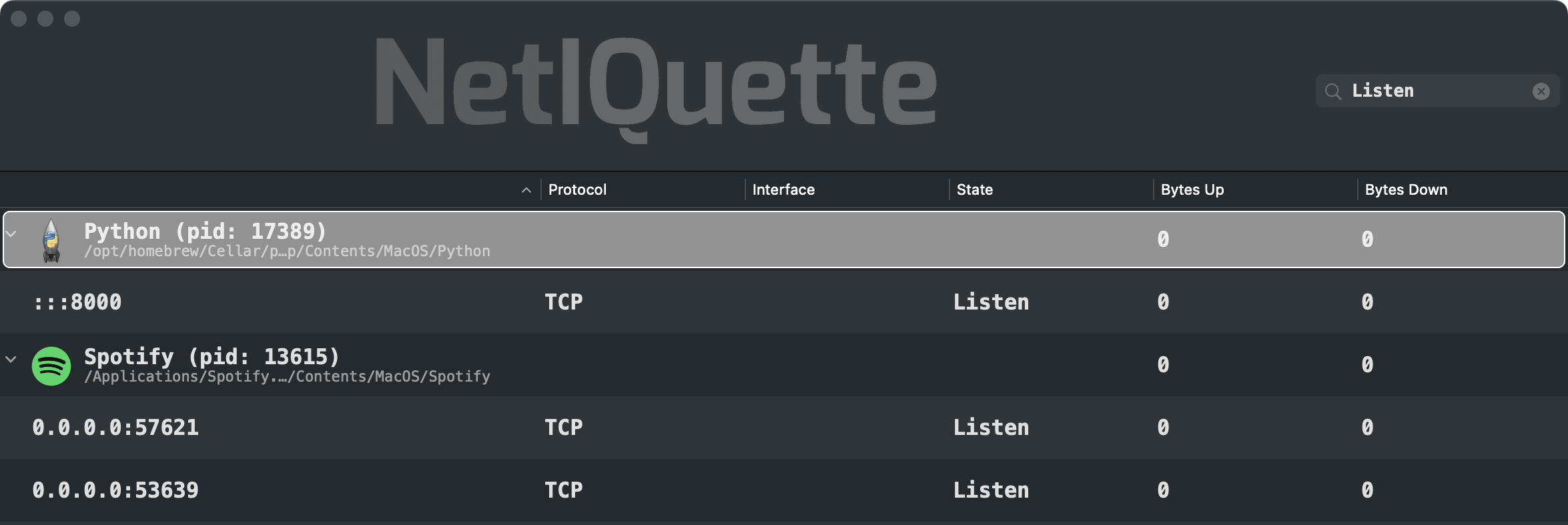
At the top (right), you'll find a filter box that can be used to narrow down displayed network connections based on criteria such as process name, path, PID, or network details like IP address, port, interface, and connection state. For example, typing 'Listen' will display all network sockets that are actively listening for potential remote connections:
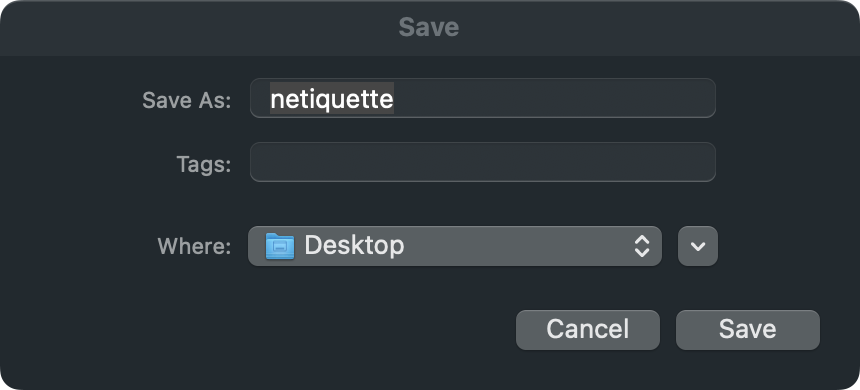
Click the 'Save' button (bottom left), to export the network activity to a JSON file:
Settings
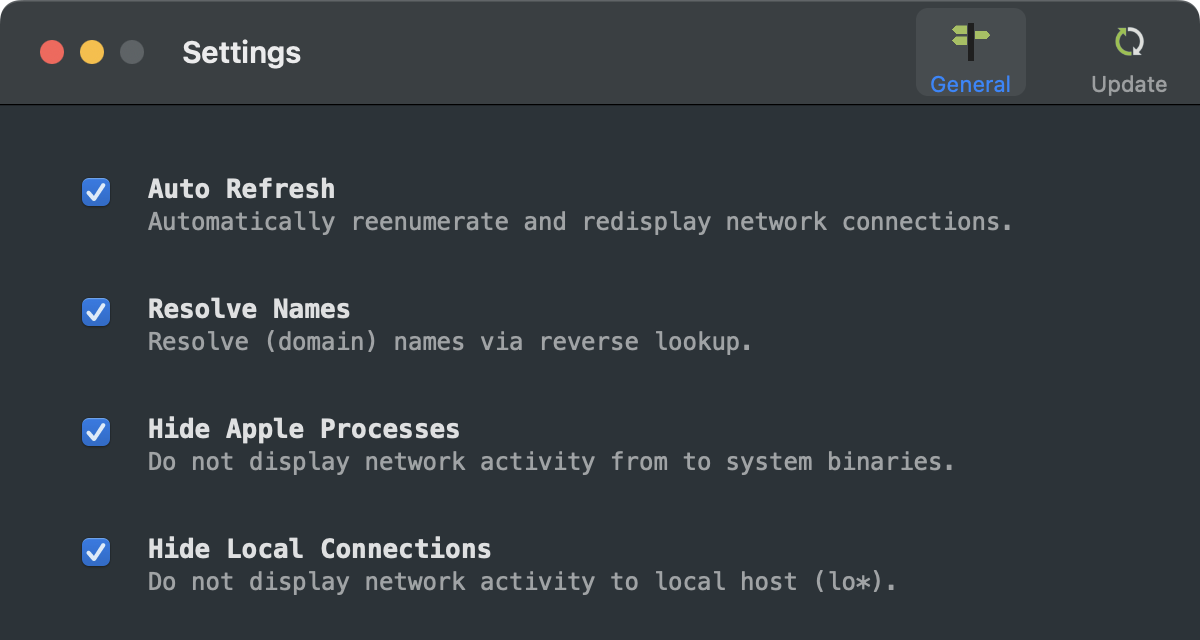
Clicking on the 'Settings' button will open the settings:
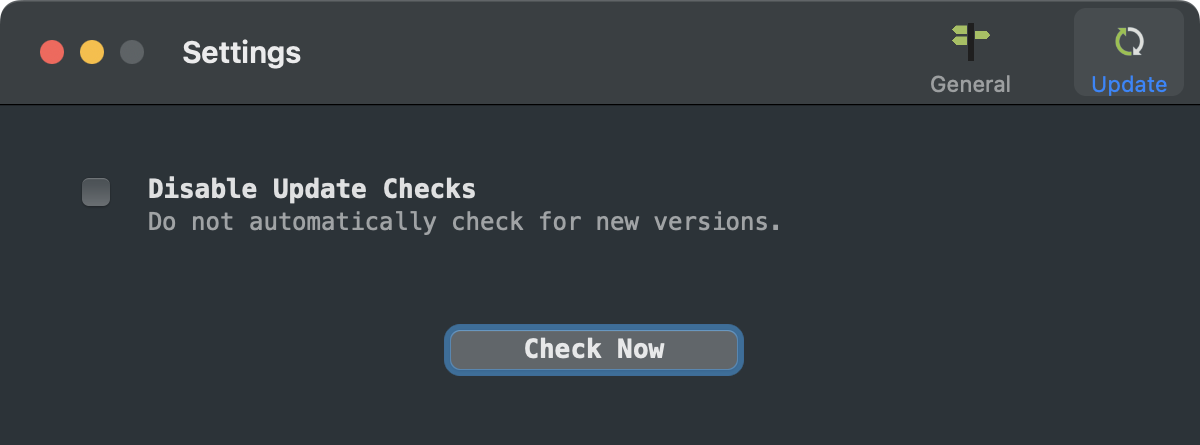
Under the 'Update' tab, you can toggle automatic update checks, as well as manually check for any updates:
Commandline Interface
Netiquette can also be run via the commandline, to list all active network connections.
Execute the Netiquette binary (note: specify the full path to the Netiquette binary within its application bundle) with -h or -help to display information about the self-explanatory commandline options:
$ Netiquette.app/Contents/MacOS/Netiquette -hNETIQUETTE USAGE: -h or -help display this usage info -list enumerate all network connections -names resolve remote host names (via DNS) -pretty JSON output is 'pretty-printed' for readability -skipApple ignore connections that belong to Apple processes
The -list commandline flag will generate a (JSON) list of all active network connections and sockets:
$ Netiquette.app/Contents/MacOS/Netiquette -list -pretty
[
{
"process" : {
"pid" : "5885",
"path" : "\/usr\/bin\/nc",
"signature(s)" : {
"signatureIdentifier" : "com.apple.nc",
"signatureStatus" : 0,
"signatureSigner" : 1,
"signatureEntitlements" : {
"com.apple.security.network.server" : true,
"com.apple.security.network.client" : true
},
"signatureAuthorities" : [
"Software Signing",
"Apple Code Signing Certification Authority",
"Apple Root CA"
]
}
},
"connections" : [
{
"remoteHostName" : "n\/a",
"protocol" : "TCP",
"interface" : "",
"localAddress" : "0.0.0.0",
"state" : "Listen",
"remotePort" : "0",
"localPort" : "666",
"remoteAddress" : "0.0.0.0"
}
]
}
...
]
Note:
To capture the output from Netiquette, simply pipe it to a file of your choice:
$ ./Netiquette.app/Contents/MacOS/Netiquette -list > /path/to/some/file.json
To capture the output from Netiquette, simply pipe it to a file of your choice:
$ ./Netiquette.app/Contents/MacOS/Netiquette -list > /path/to/some/file.json